Secure Your Network Perimeter
Against File-Based Threats
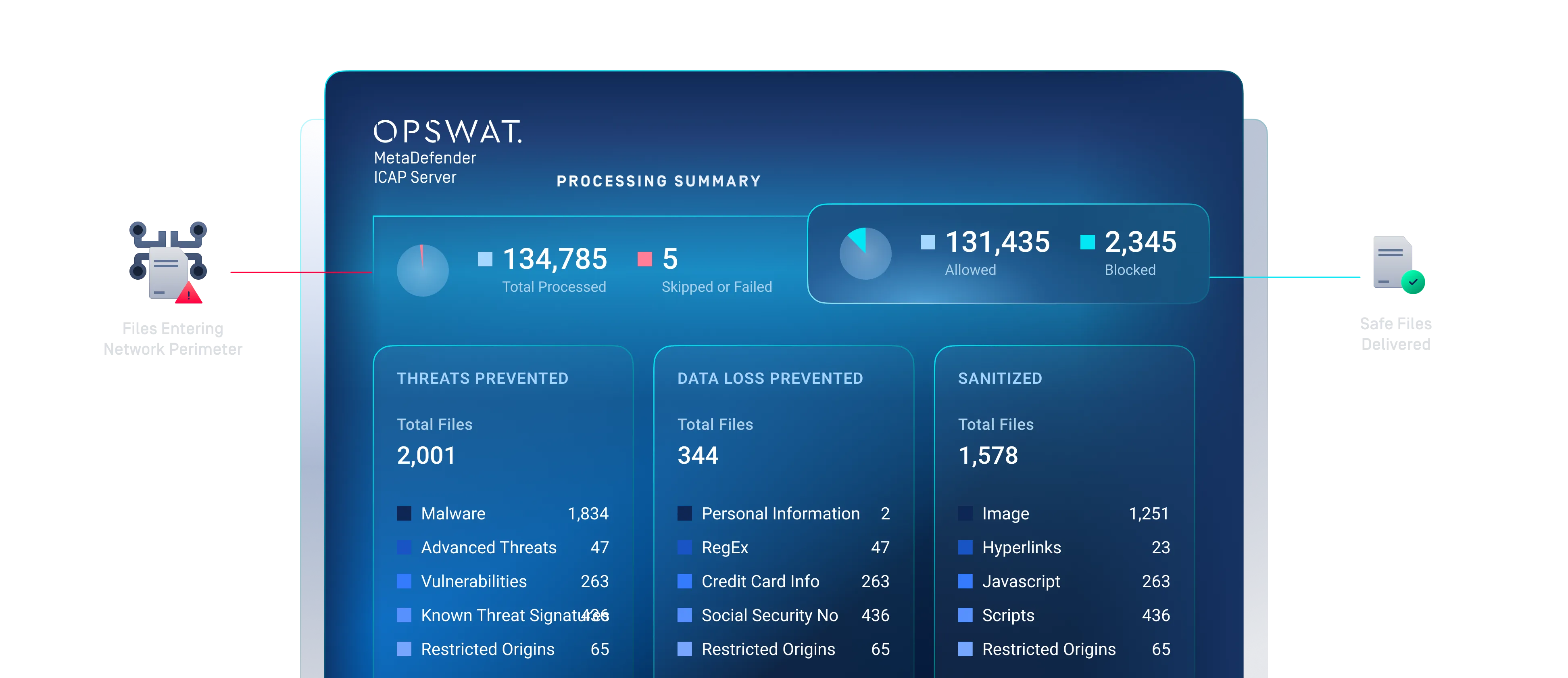
MetaDefender ICAP Server is OPSWAT’s ICAP antivirus scanning and network perimeter file security solution for inspecting files before they enter your network. It integrates with ICAP-enabled appliances such as WAFs, load balancers, proxies, and managed file transfers (MFTs) to support malware prevention and data loss protection without requiring architectural changes, supporting layered file security across transfer and inspection workflows.
- 威胁预防
- 无缝集成
- 优化性能
OPSWAT 得到以下机构的信任
Protect Your Systems and Users
MetaDefender ICAP Server employs a "zero trust" strategy to secure your systems and users by inspecting file content at the network level, blocking threats, or sanitizing files traveling through your network traffic.
Secure
检测并阻止零时差和高级规避型恶意软件。
符合要求
保护敏感数据,帮助符合法规要求。
可扩展
扫描大量文件,无集成难题。
多用途
可在 10 分钟内与任何支持ICAP 的安全设备集成。
主要特点与优势
Multi-Layered File Security
Built-in threat detection and prevention protects web applications from malware, zero-day attacks, data loss, and file-based threats using OPSWAT’s multi-layered technologies.
Broad Compatibility
Add a layer of advanced file security to virtually any network device you already use — with the broadest compatibility in the market and validated integrations across OPSWAT partners including WAFs, load balancers, ingress controllers, next-gen firewalls, ADCs, and proxies.
遵守规定
Prevent sensitive or out-of-policy data breaches to meet compliance requirements like ISO 27001, PCI-DSS, HIPAA, and GDPR, while preventing penalties and maintaining customer trust.
Flexible and Scalable Deployments
Reduce overhead with lightweight ICAP integration in under 10 minutes. Fits any IT infrastructure with flexible on-premises, hybrid, and cloud deployments, so organizations can focus on file security without major architectural changes.
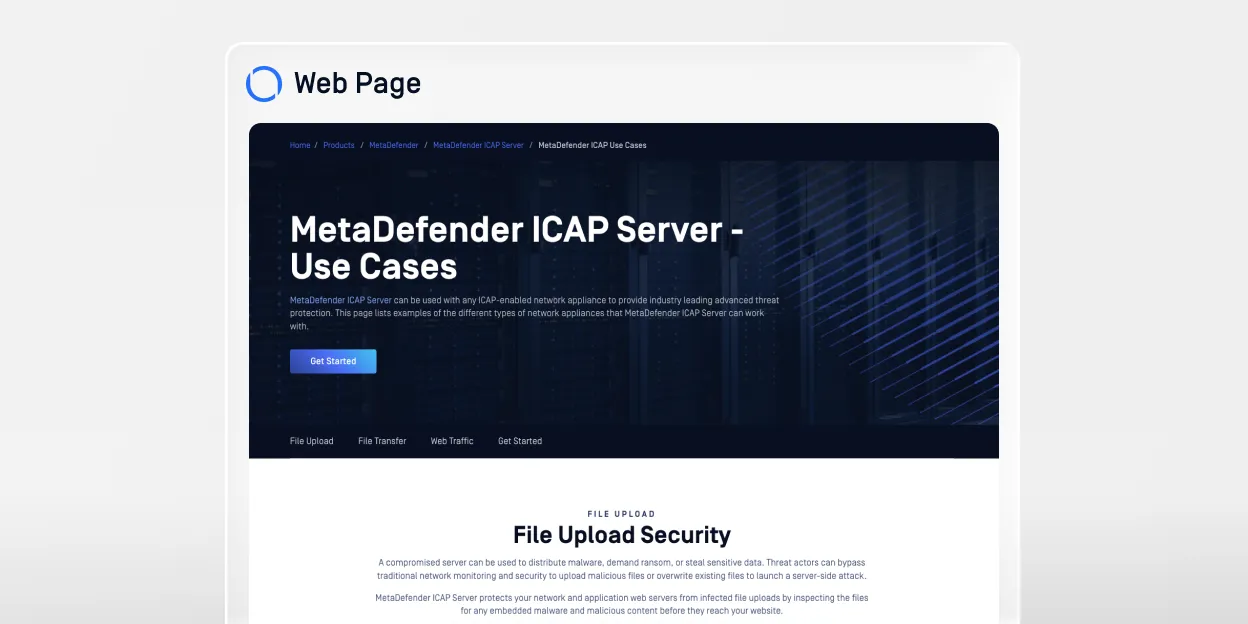
使用案例
Works With Your Existing
Network Infrastructure
MetaDefender ICAP Server slots into your existing network infrastructure to scan and process every file before it reaches your users – no major changes required. ICAP is a lightweight, standardized protocol that makes it efficient to add antivirus scanning and other security solutions to your existing setup.

Certified Integrations with Industry Leaders
Through validated partnerships with trusted technology providers, organizations can deploy advanced file security directly within their existing network architecture.
From Traffic Interception to Clean Delivery
Each step protects network traffic and file exchanges through a policy-driven ICAP workflow that inspects and blocks or sanitizes threats before release, ensuring real-time security, compliance, and seamless integration without impacting performance.

Multi-Layered
Threat Prevention for Network Traffic
值得信赖
2,000+
Organizations Worldwide
30+
AV Engines for Malware Detection
Prevent
Zero-Day Exploits and Evasive Malware
数据丢失预防(DLP)
Integrates With Industry-Leading Devices in 10 Minutes
Scalable for Enterprise Environments
From On-Premises to Cloud Deployment
灵活、可扩展的MetaDefender ICAP Server 解决方案可与您现有的IT 基础设施集成--无论是内部部署、现代架构,还是通过软件即服务。
Proven Protection for the World’s Most
Secure Environments

OPSWAT 多年来一直是F5值得信赖的合作伙伴,提供先进的文件安全性,与F5应用交付和安全平台(ADSP)相辅相成。通过将OPSWAT的MetaDefender 与 F5 ADSP 集成,客户可受益于无缝、一致的安全性,同时在任何地点、任何外形尺寸上交付应用程序和 API 并确保其安全。我们将共同为企业创造价值,帮助他们降低风险、确保合规性并保护关键数据。
Built to Support Regulatory and Industry Compliance
三步轻松入门
部署和使用

资源
常见问题
MetaDefender ICAP Server provides inline inspection of file-based network traffic using the ICAP protocol to detect malware, prevent data leakage, and enforce security policies in real time.
It integrates with ICAP-compatible devices such as web application firewalls (WAFs), proxies, load balancers, next-generation firewalls, and managed file transfer solutions.
It applies OPSWAT’s multi-layered protection, including Multiscanning, Deep CDR™ Technology, Proactive DLP, and Adaptive Sandbox.
Yes. It supports ICAP request and response modes, enabling inspection of files entering and leaving the network based on defined security policies.
MetaDefender ICAP Server can be deployed in on-premises, hybrid, or cloud environments and integrates seamlessly into existing network architectures with minimal operational impact.