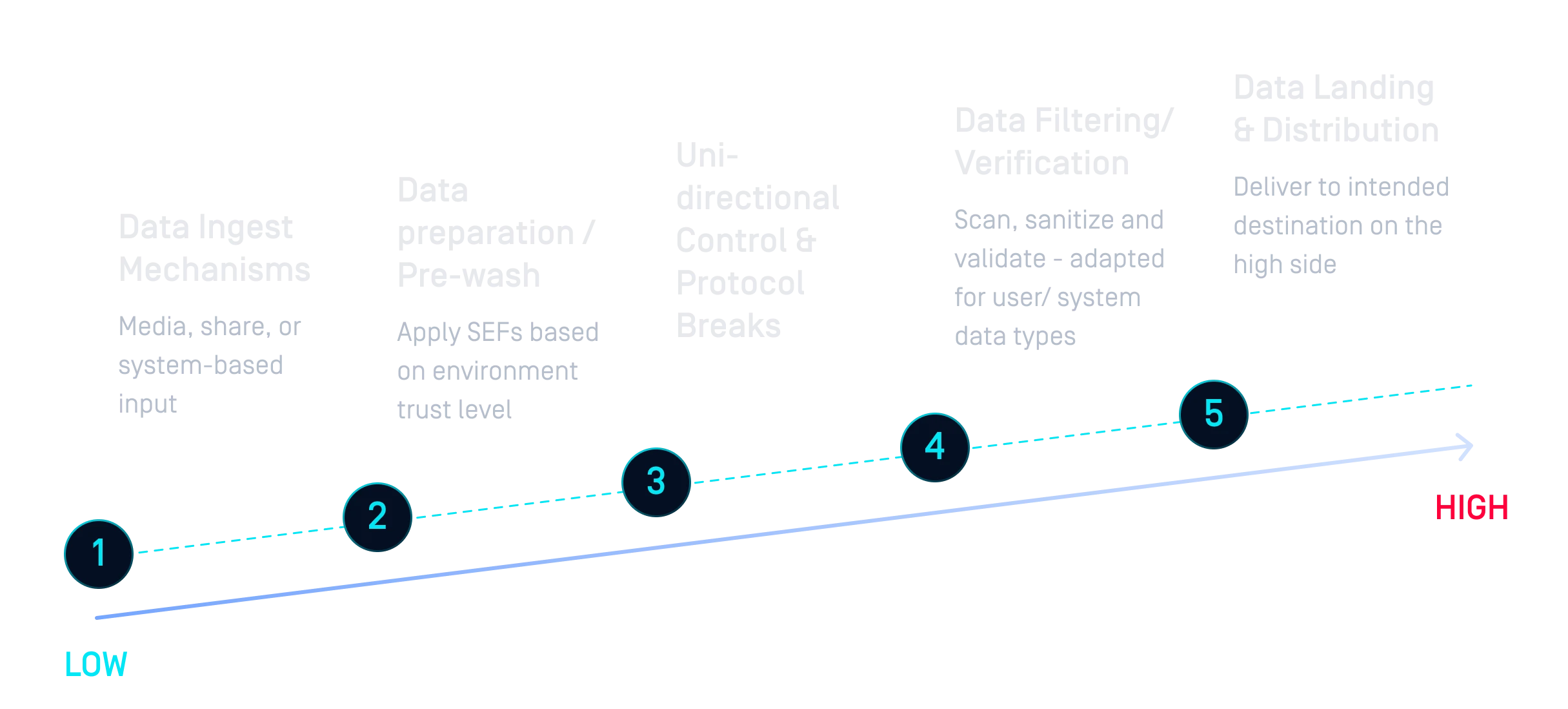
进口(低→高)
- 防止恶意软件进入机密网络。
- 融合Multiscanning、Adaptive Sandbox 、深度CDR™技术、单向控制与协议中断功能。
OPSWAT 解决方案是一款模块化跨域安全解决方案,旨在确保在不同信任级别和保密等级的网络之间安全传输数据。该方案基于MetaDefender 构建,融合了高级威胁防护、数据单向通道和安全网关功能,用于实施数据输入输出控制,防范恶意软件和数据泄露,并为国防、情报及关键基础设施环境提供符合合规要求的工作流程支持。


现在,跨域移动的数据量大、格式多样,从日常用户文件到地理空间数据、安装程序和应用程序更新,不一而足。传统系统和纯硬件系统难以处理这些数据,也无法以灵活、可扩展的方式提供所需的安全执行功能(SEF)。
系统必须能够抵御高度机智的攻击者,包括民族国家的威胁。安全级别之间的数据传输暴露了传统防御系统无法解决的漏洞,而人工智能驱动的攻击则需要现代化的自适应保护。

永久隔离数据已无法满足跨地域协作的需求。现代 CDS 系统必须适应业务需求,支持不同的数据量、数据类型和应用,同时实现API API 以及云到企业内部的无缝传输。
OPSWAT 提供了一种模块化、以软件为主导的方法,可增加现有流程,
,并采用市场领先的技术。
OPSWAT拥有市场领先的技术和插入/拔出功能,其模块化方法是构建 CDS 解决方案的更有效方式。
利用仿真沙箱,企业可以查看操作系统补丁或应用程序等复杂数据类型中的 IOC,并消除潜在的威胁载体。
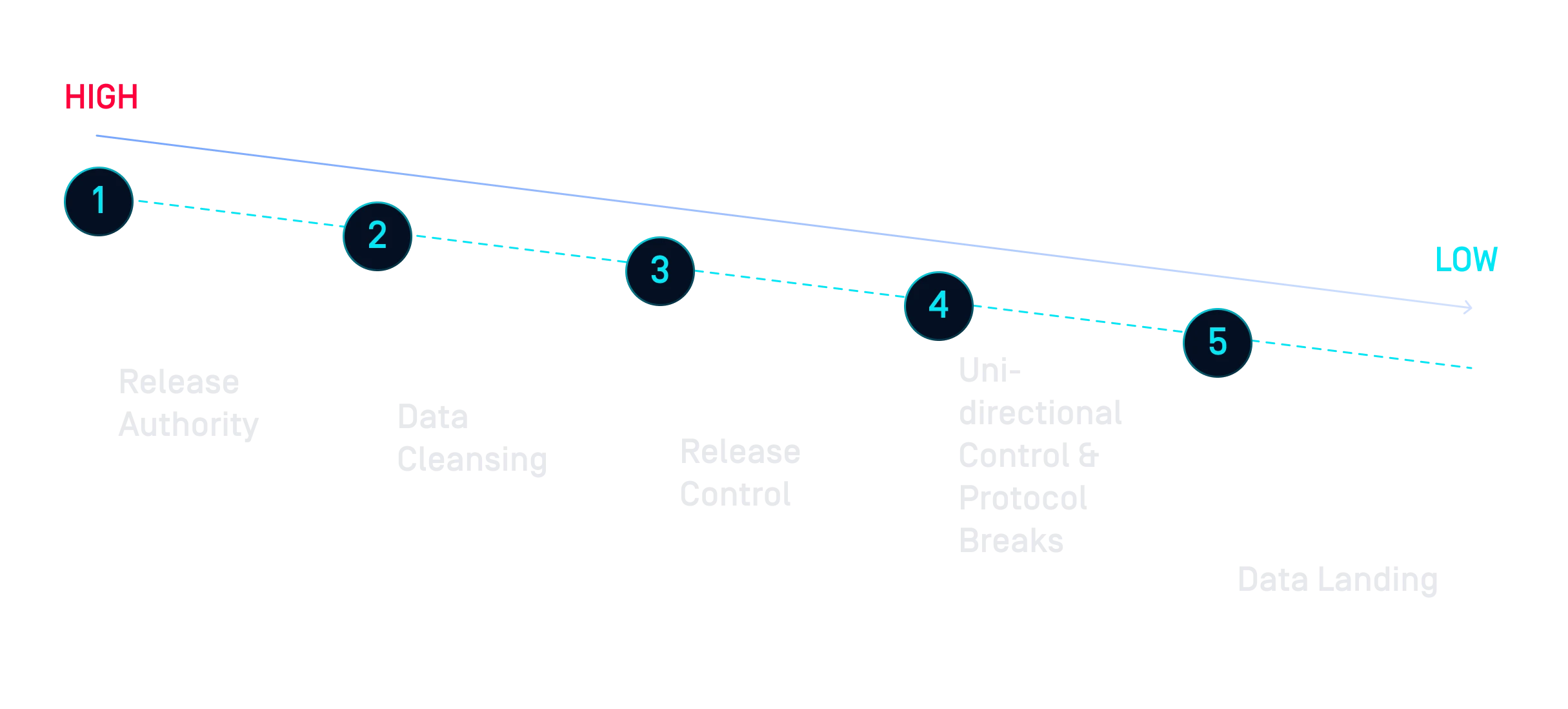
Proactive DLP 可通过检测和阻止文件中的敏感信息,帮助确保从较高分类向较低分类传输的数据(如与合作伙伴共享的报告)不包含不打算发布的敏感信息。
有了MetaDefender Kiosk,来自可移动Media 的数据就可以根据贵组织的风险态势通过适当的安全执行机制。
一个主要优势是,将 MDCore 与MFT 等工具结合使用,可以实现完整的审计跟踪,使组织能够追溯并查看是哪个角色或人物试图外泄数据。
传统的空中封闭方法会隔离数据并使协作变得困难,而OPSWAT的解决方案则不同,它可集成到跨域架构中并执行安全策略。软硬件混合方法支持多个利益群体,同时确保敏感数据得到适当控制、监控和审计。
随着网络攻击和实施网络攻击的威胁者变得越来越复杂,世界各地的管理机构都在实施相关法规,以确保关键基础设施采取必要的措施来保证安全。