Secure File Movement Across Enterprise
Trust Boundaries
Protect sensitive data as it moves across IT, OT, cloud, and partner environments with policy-driven controls, deep inspection, and
compliance-aligned governance.
- Cross-Domain Protection
- Risk-Based Controls
- 合规调整

OPSWAT 得到以下机构的信任
Why Enterprise File Movement Creates Hidden Risk
File Transfers Bypass Security Boundaries
Files frequently move between users, networks, cloud platforms, and operational systems without deep inspection, allowing malware, zero-day exploits, and embedded payloads to cross trust zones undetected.

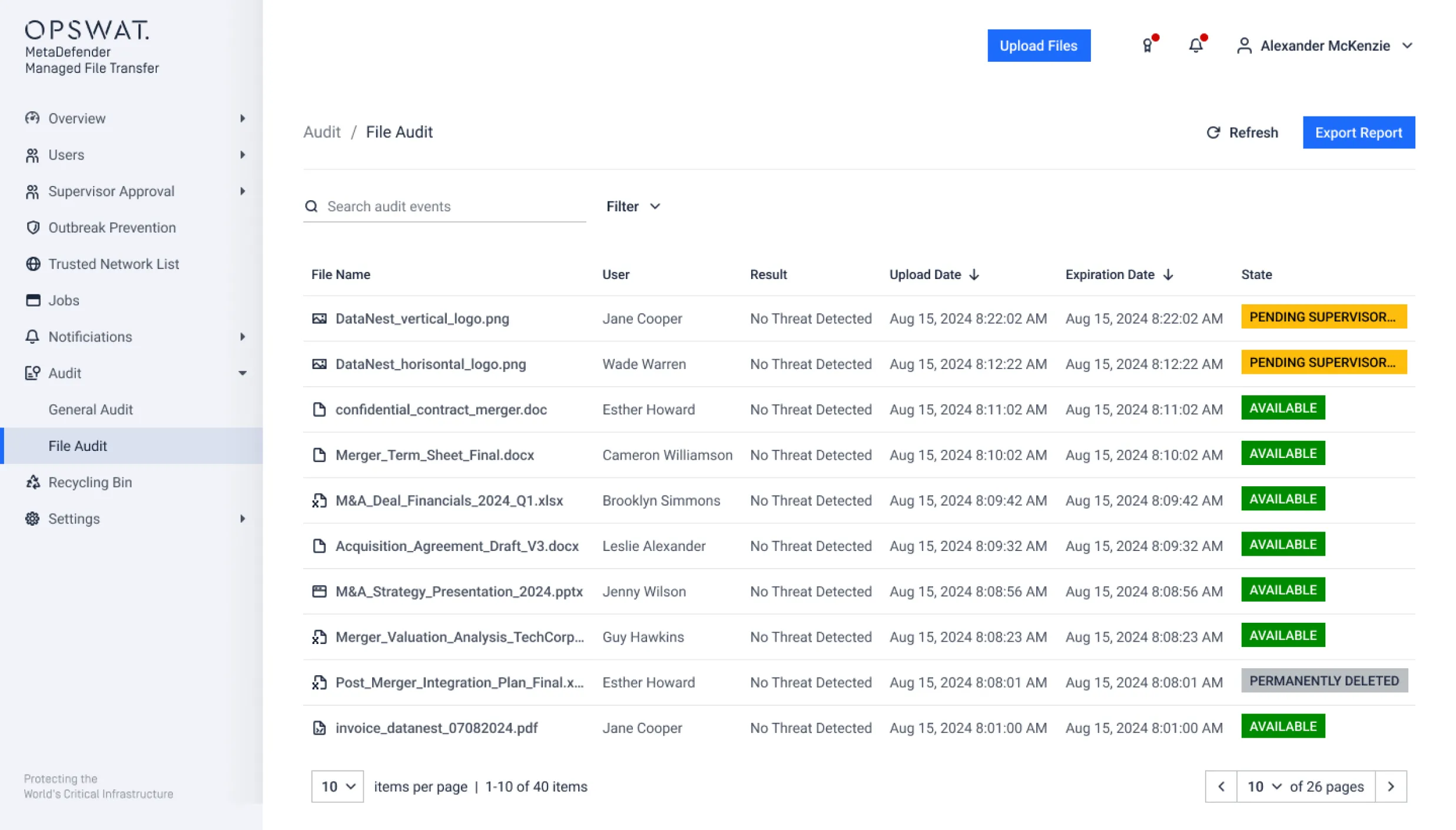
Audit Gaps Across File Workflows
Organizations must demonstrate control over how files are accessed, routed, approved, and stored. Disconnected tools create blind spots in policy enforcement and regulatory reporting.

IT–OT and Cross-Domain Exposure
In regulated and industrial environments, file exchange between security domains introduces risk. Without embedded inspection and enforcement, file-based threats can propagate laterally across systems.
A Security-Embedded Approach to
Enterprise File Movement
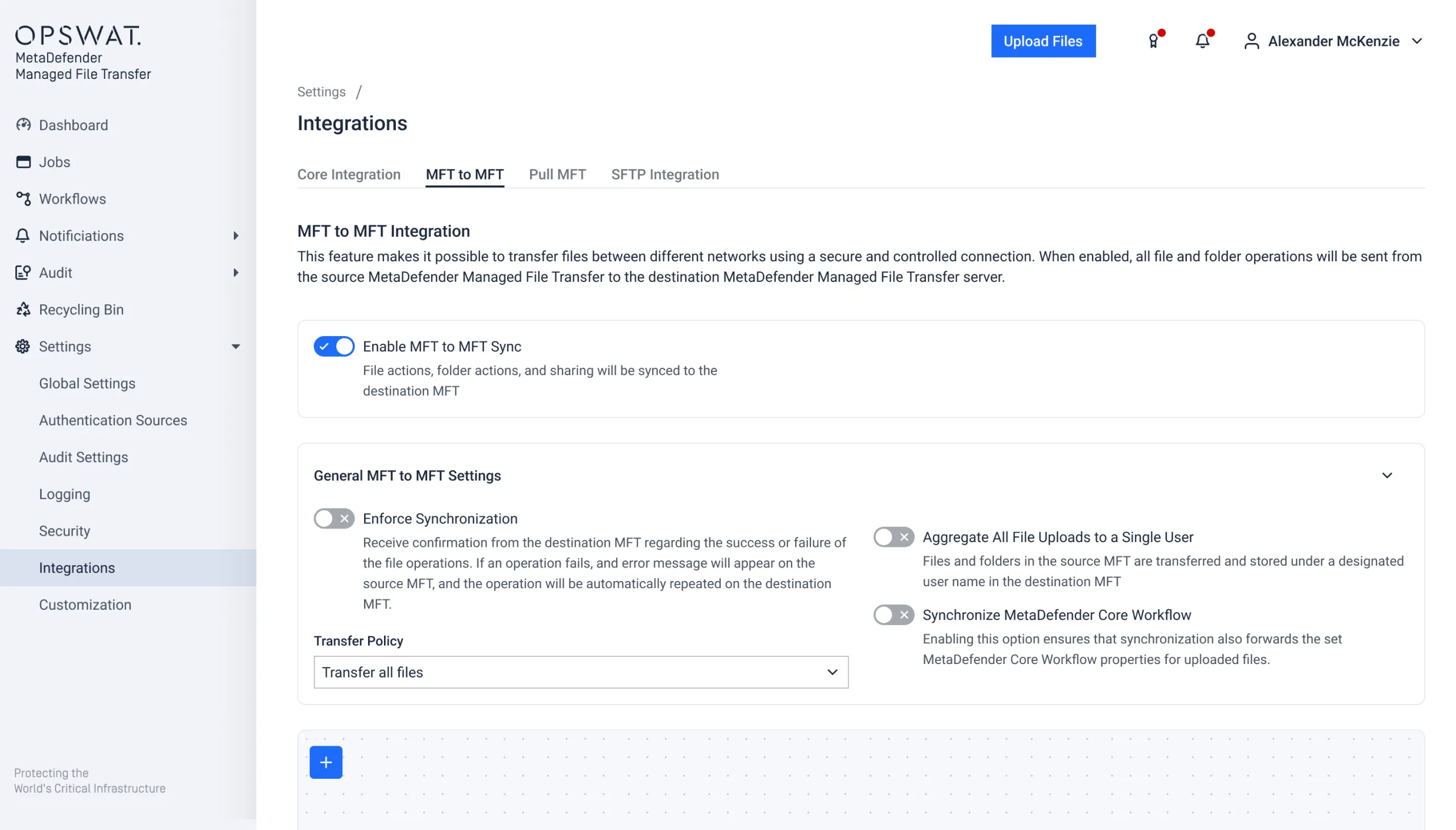
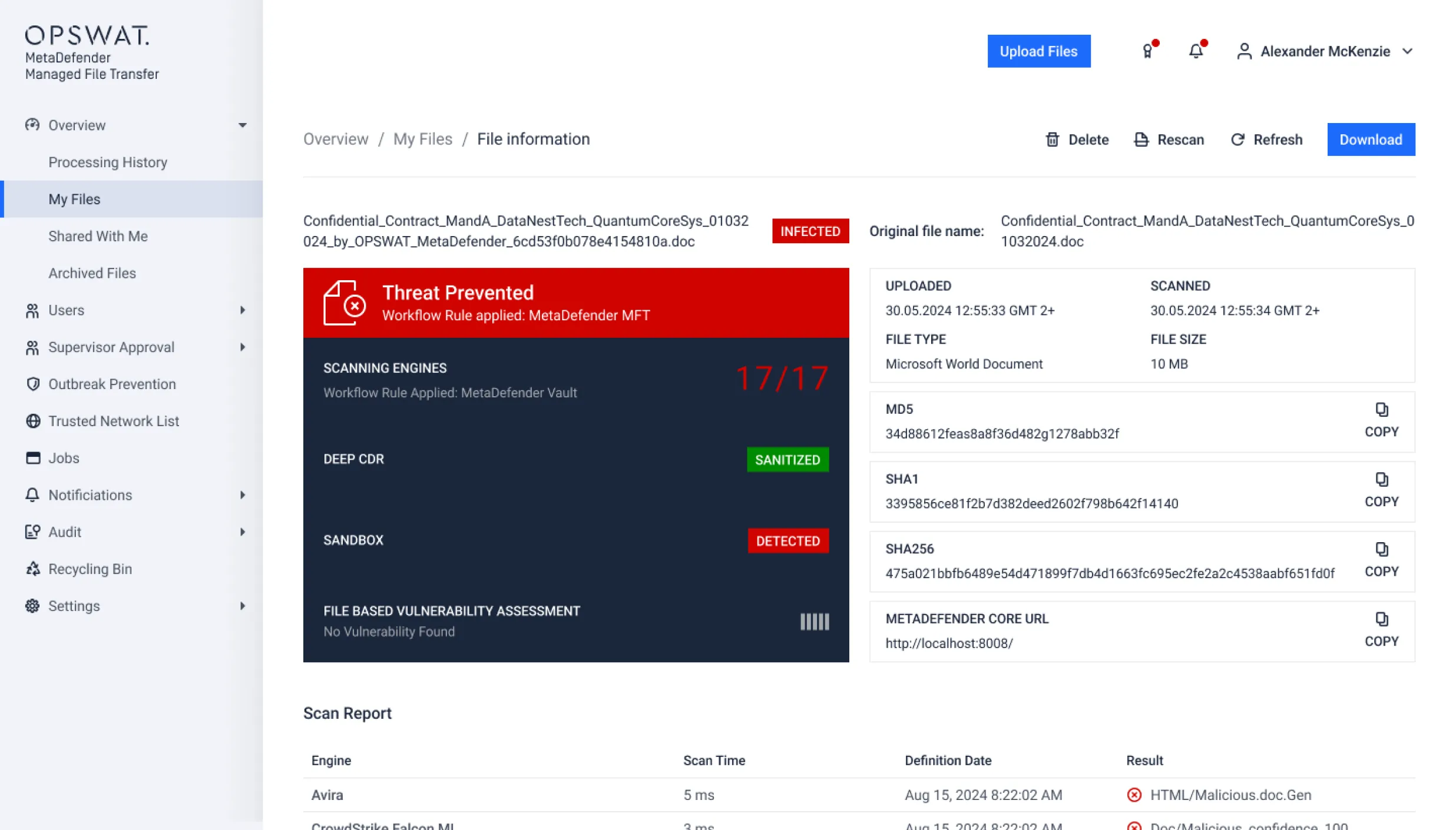
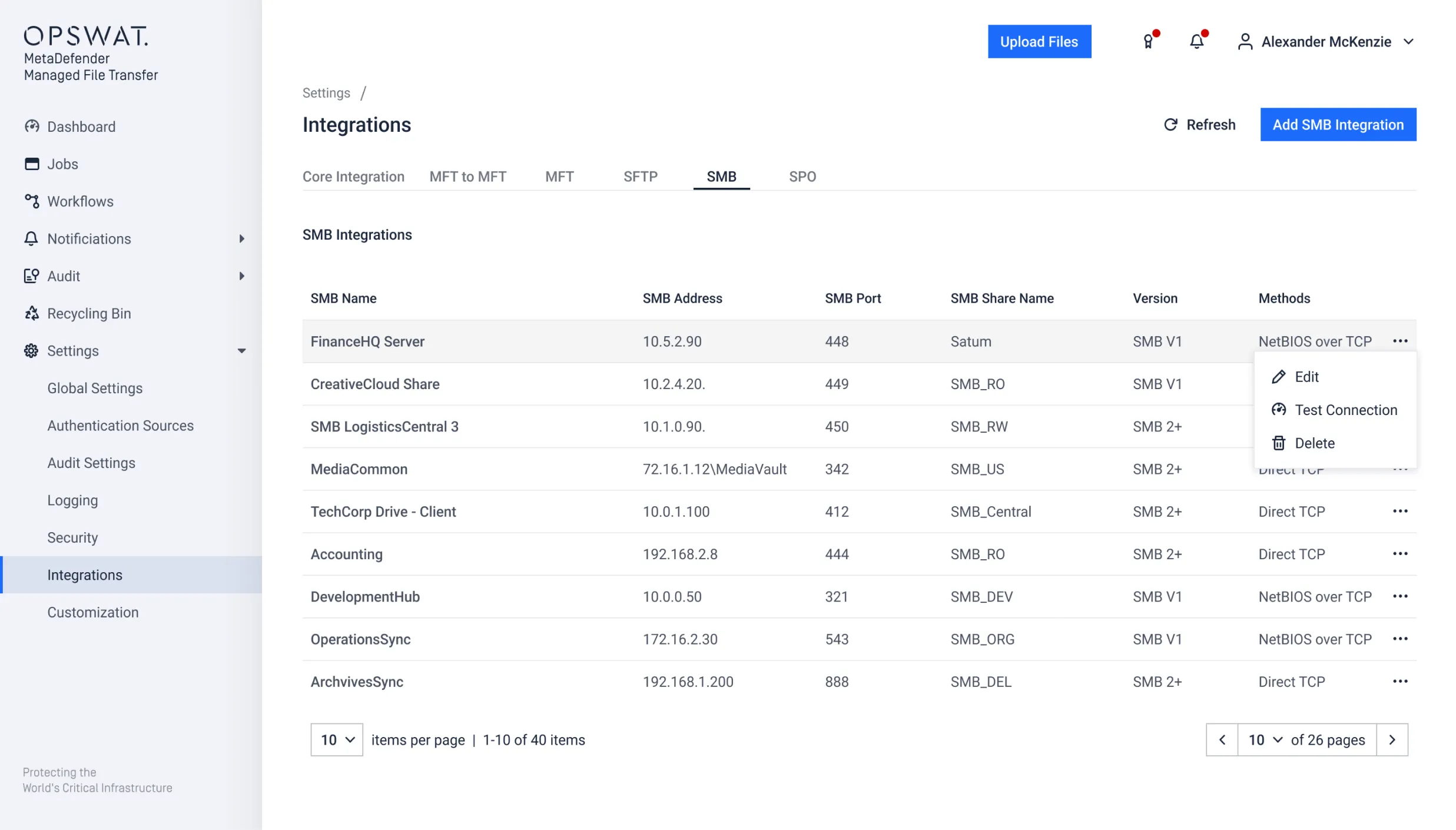
OPSWAT enables organizations to secure file exchange across trust boundaries with MetaDefender Managed File Transfer (MFT), combining embedded inspection, policy enforcement, and centralized governance, AI-powered malware detection using Predictive Alin AI for pre-execution zero-day detection of file-based threats before transfer.
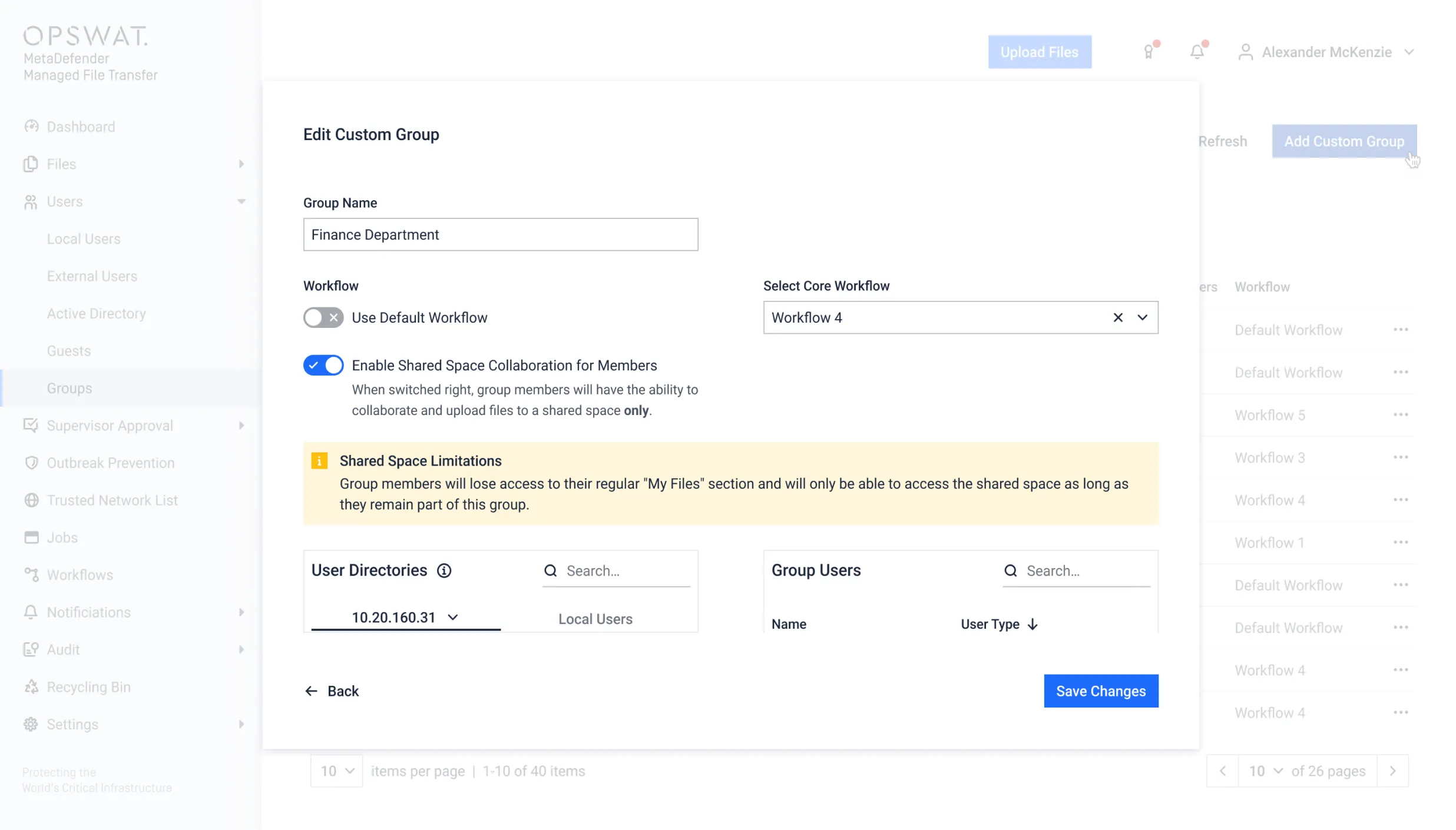
主要功能
Cross-Domain File Control
Control file movement between low- and high-security environments using defined trust policies, ensuring sensitive or untrusted files cannot bypass security checkpoints.
Risk-Based Workflow Enforcement
Automate file routing decisions based on inspection results, including AI-powered malware detection, metadata classification, and organizational policy to reduce manual error and enforce consistent governance.
Segmented Environment Support
Apply consistent controls across enterprise IT, operational technology (OT), cloud, and partner ecosystems, reducing lateral movement risk across security domains.
- MetaDefender Managed File Transfer
- MetaDefender Managed File Transfer
- MetaDefender Managed File Transfer
Centralized Policy Governance
Standardize enforcement across business units, subsidiaries, and global operations through unified policy management and audit visibility.
Comprehensive Audit Logging
Maintain comprehensive records of file activity and enforcement decisions to support frameworks such as HIPAA, GDPR, NIS2, PCI, FISMA, and NIST.
- MetaDefender Managed File Transfer
- MetaDefender Managed File Transfer
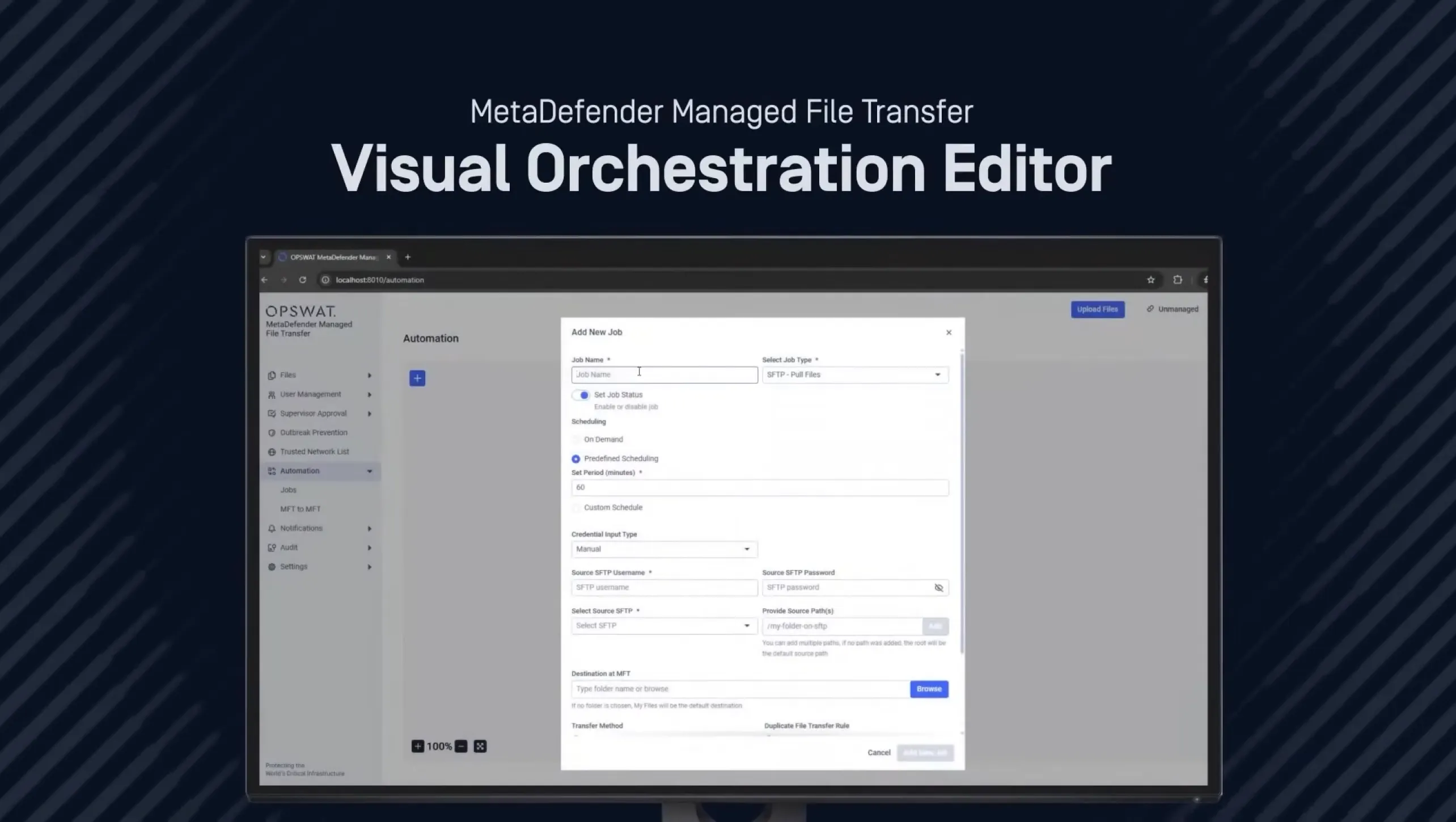
See MetaDefender Managed File Transfer in Action
Watch how MetaDefender Managed File Transfer (MFT) secures file exchange with embedded threat prevention, policy enforcement, workflow automation, and centralized visibility across IT and OT environments.
播放列表
3个视频- MetaDefender Managed File Transfer (MFT) Product Overview
- Simplify Secure File Transfers with the New Visual Orchestration Editor | MetaDefender MFT
- Live Demo: See How OPSWAT Managed File Transfer Stops Live Malware in Information Technology
MFT Market Leader in G2 Spring 2026 Report
Securing File Movement in High-Risk Industries
Organizations operating across regulated, segmented, and critical infrastructure environments must secure how files move between systems, users, and security zones. Embedded inspection and policy enforcement help prevent file-based threats from disrupting operations or exposing sensitive data.
能源与公用事业
Energy operators routinely move engineering files, configuration updates, and operational reports between corporate IT and industrial control networks. Without inspection at transfer points, file-based threats can cross into OT environments and disrupt operations. Securing file movement across trust boundaries helps reduce cyber-physical risk while maintaining operational continuity.

制造业
Manufacturers exchange production files, firmware updates, and supplier data across segmented environments. A single infected file can spread laterally across plant systems. Enforcing inspection checkpoints and policy-driven routing reduces the risk of operational downtime caused by file-borne threats.

政府
Government agencies manage sensitive and classified information across internal departments and external partners. Secure file movement requires enforceable approval workflows, traceable audit trails, and controlled routing across security domains to meet national security and regulatory mandates.

财务
Financial institutions transfer reports, customer data, transaction files, and third-party documents daily. Without centralized visibility and risk-based controls, organizations face compliance gaps and potential data exposure. Secure file governance supports alignment with financial regulations and data protection laws.

医疗保健
Healthcare organizations exchange patient records, imaging files, and billing data between providers, insurers, and cloud systems. Enforcing inspection, encryption, and documented access controls reduces the risk of PHI exposure while supporting HIPAA and data protection compliance.

Media & Entertainment
Media organizations transfer large video and creative assets across global production teams and partners. Embedded security controls protect intellectual property from tampering, hidden malware, or unauthorized redistribution during file exchange.

随处部署,随处集成
Scalable, comprehensive managed file transfer solution that integrates seamlessly and follows your files wherever they go.

企业内部
Secure internal and air-gapped file exchange within regulated and industrial networks.

Cloud
Protect file workflows across SaaS platforms, cloud storage, and distributed teams.

混合动力
Enforce consistent security and governance across mixed IT, OT, and cloud infrastructure.
客户成功
Designed for Regulatory and
Operational Accountability
Enterprise file movement must align with data protection, industry mandates, and audit requirements. OPSWAT enables enforceable policies, inspection checkpoints, and documented controls that support HIPAA, GDPR, NIS2, PCI, FISMA, and NIST compliance initiatives.
资源

MetaDefender Managed File Transfer MFT)产品数据表

MetaDefender Managed File Transfer MFT)解决方案简介
MetaDefender Managed File Transfer MFT) 博客
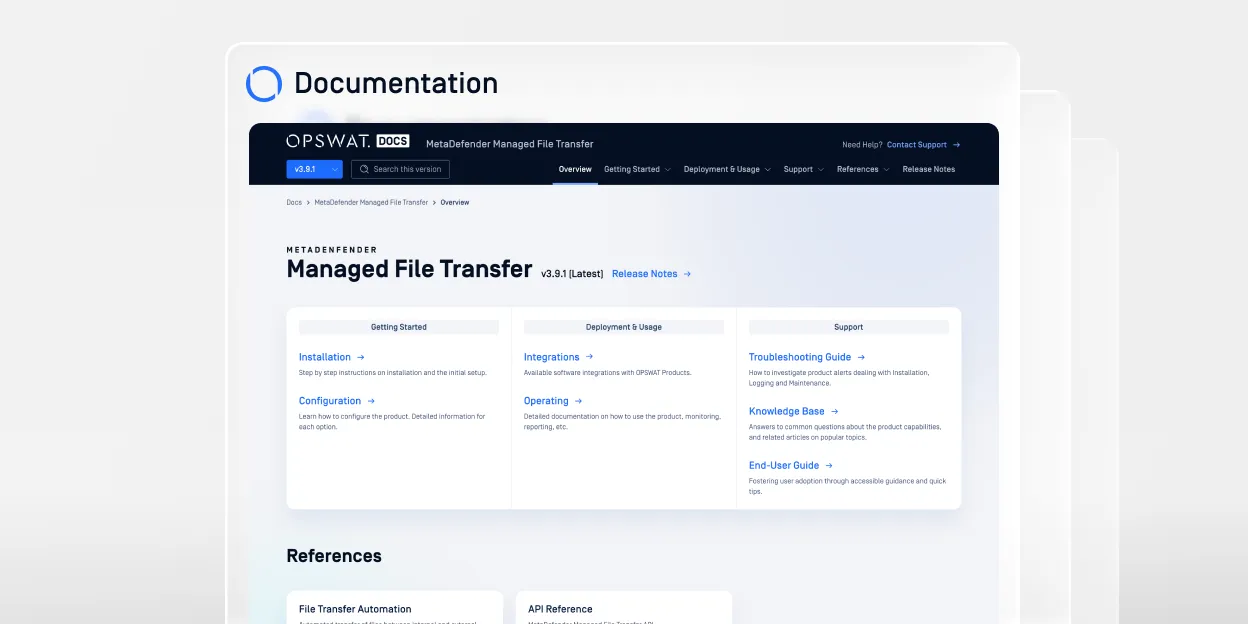
MetaDefender Managed File Transfer MFT) 文档
在发现零日漏洞后,通过MetaDefender Managed File Transfer MFT)保障合作伙伴文件交换安全

Secure Managed File Transfer终极指南
0 条结果。请重试。
常见问题解答
When files move between users, systems, or security zones, they can carry hidden malware, embedded scripts, or unauthorized data. In cross-domain environments—such as IT to OT or internal to external partner networks— inspection before transfer, including AI-powered malware detection using Predictive Alin AI, helps detect known and zero-day threats before they bypass perimeter defenses and spread laterally.
File-based attacks often begin with a malicious attachment or compromised document. When that file is shared across departments, cloud platforms, or operational systems without inspection, the embedded payload can execute in new environments. Securing file movement reduces this lateral propagation risk.
Encryption protects data in transit from interception, but it does not analyze the file’s contents. An encrypted malicious file can still reach its destination safely—and execute once opened. Effective file security requires inspection and policy enforcement in addition to encryption.
Operational technology environments often lack the same endpoint protections found in enterprise IT systems. If an infected file crosses into OT networks, it can impact industrial control systems, production lines, or critical infrastructure. Securing IT–OT file movement helps reduce cyber-physical risk.
Compliance frameworks require visibility into how data is accessed, transferred, and stored. Implementing enforceable policies, documented approvals, and centralized audit logging helps demonstrate control over file movement and reduces regulatory exposure.
Basic file transfer focuses on moving data from one location to another. Secure file governance adds inspection, policy enforcement, access controls, and traceable logging to ensure files are moved safely and in alignment with organizational and regulatory requirements.
Zero-trust models assume no file, user, or system should be inherently trusted. Applying inspection and policy controls at file transfer checkpoints ensures that every file crossing a trust boundary is verified before being allowed into sensitive environments.
Organizations should reassess file transfer security when:
- Expanding cloud or hybrid environments
- Connecting IT and OT networks
- Engaging new external partners